Virtual – Excel 365 Level 3
03/17/2026 from 09:00 AM - 05:00 PM Simple Description: Master Excel 365 with advanced formulas, macros, and collaboration tools. Great For: Advanced Excel users, analysts, professionals automating or sharing data. […]
03/17/2026 from 09:00 AM - 05:00 PM Simple Description: Master Excel 365 with advanced formulas, macros, and collaboration tools. Great For: Advanced Excel users, analysts, professionals automating or sharing data. […]
Description In this course you will cover how to develop web applications that aren’t subject to common vulnerabilities, and how to test and validate that their applications are secure, reliable […]
Description In this course, you will cover the implementation and analysis of the IS18 Top Controls. These controls have been identified as critical by leading government and private organizations with […]
Description From networking and cybersecurity essentials to hardware and software basics, IT Fundamentals demonstrates your readiness for the digital workplace. The CompTIA IT Fundamentals certification is designed to help you […]
Description This course presents an approach for dealing with security and privacy throughout the entire software development lifecycle. You will learn about vulnerabilities that undermine security, and how to identify […]
Description This course will cover understanding how to plan, create and utilize their systems. Prevent, detect and respond to attacks through the use of hands-on labs in our exclusive Cyber […]
Description In this course you will cover 20+ modules of network forensic topics. The C)NFE provides practical experience through our lab exercises that simulate real-world scenarios covering investigation and recovery […]
Description This 4-hour course and associated credential (IOZ-110) will validate a participant’s knowledge of IoT terminology, their ability to understand the components of IoT infrastructure, uncover challenges for consideration and […]
Description In this course, you will cover what you can do to protect yourself and your organization from technology-related risks. This course will help you to: Understand both security and […]
Description In this course you will cover the keys to being a Powershell hacker. Most companies have an Active Directory infrastructure that manages authentication and authorization to most devices and […]
Description In this course, you will cover the process of certifying, reviewing and accrediting an information system(IS). What does it take to have a certified and accredited information system in […]
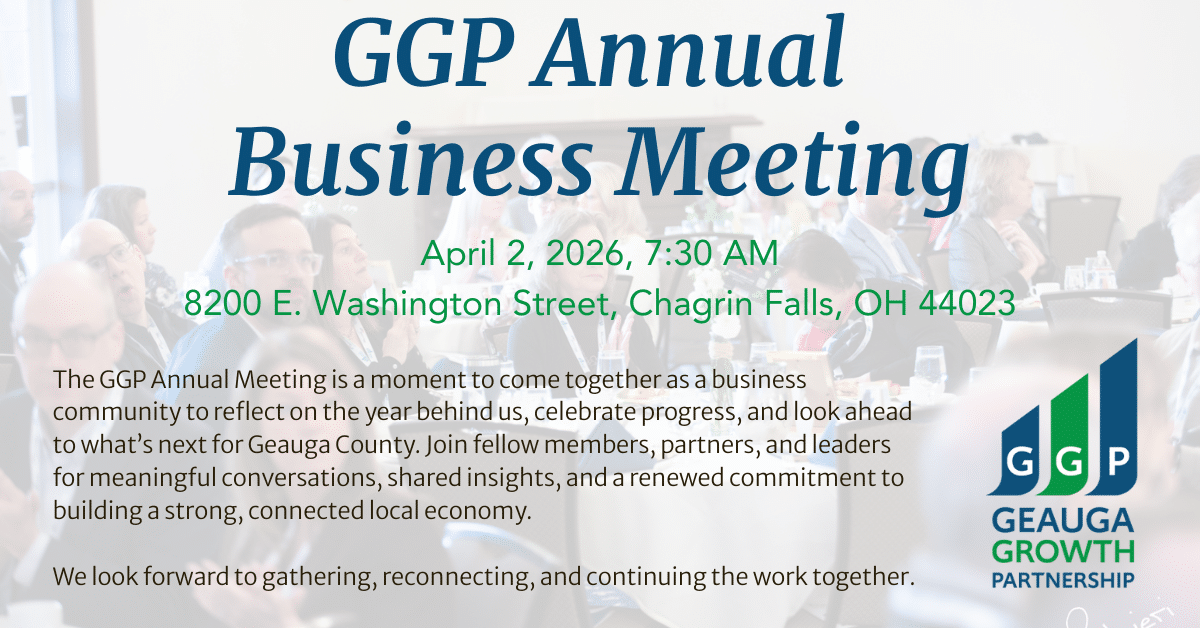
We are delighted to invite you to the 2026 Geauga Growth Partnership Annual Meeting, where we’ll come together as a business community to reflect on the year behind us, celebrate […]