C)PSH: Certified PowerShell Hacker
Description In this course you will cover the keys to being a Powershell hacker. Most companies have an Active Directory infrastructure that manages authentication and authorization to most devices and […]
Description In this course you will cover the keys to being a Powershell hacker. Most companies have an Active Directory infrastructure that manages authentication and authorization to most devices and […]
Description In this course, you will cover the process of certifying, reviewing and accrediting an information system(IS). What does it take to have a certified and accredited information system in […]
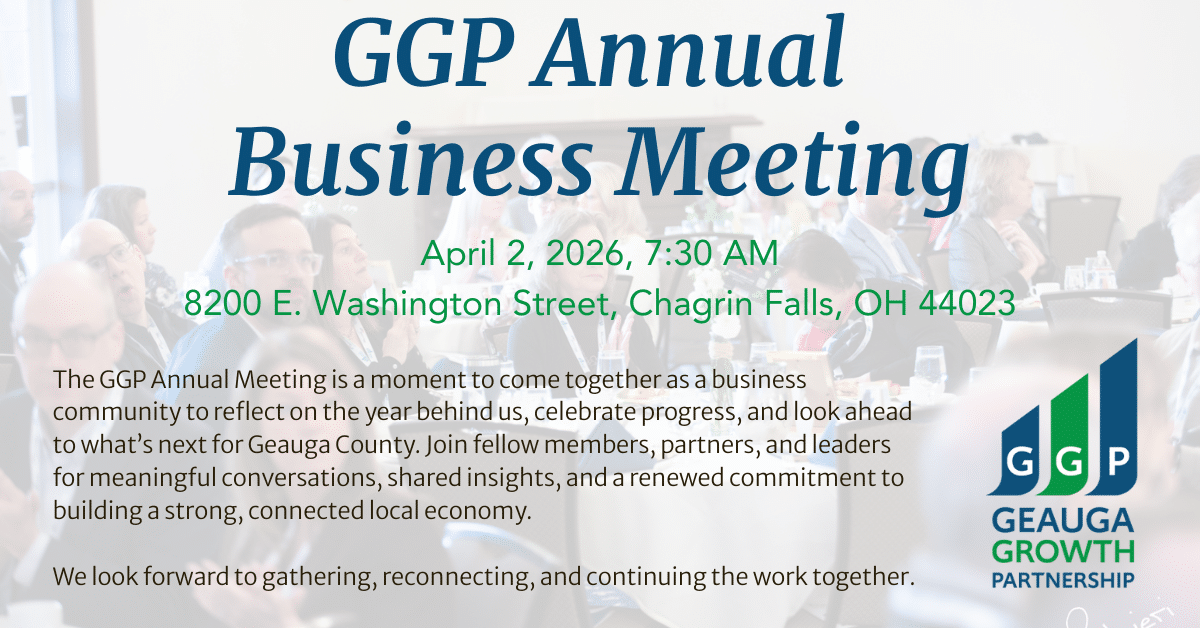
We are delighted to invite you to the 2026 Geauga Growth Partnership Annual Meeting, where we’ll come together as a business community to reflect on the year behind us, celebrate […]
Join us for the April Geauga Economic Leadership (G.E.L.) breakfast on Friday, April 3, 2026, co-sponsored by Geauga Growth Partnership and Kent State University at Geauga. This monthly breakfast series […]
Description This course will provide foundational level knowledge of cloud services and how those services are provided with Microsoft Azure. The course can be taken as an optional first step […]
Description If you are look for the "gotta have it" cybersecurity course, then the Certified Information Systems Security Officer is for you. The C)ISSO will prepare you with a broad […]
Description Artificial intelligence (AI) and machine learning (ML) have become an essential part of the toolset for many organizations. When used effectively, these tools provide actionable insights that drive critical […]
Description This course covers the duties of cybersecurity analysts who are responsible for monitoring and detecting security incidents in information systems and networks, and for executing a proper response to […]
Description In this course, you will cover: This course provides a comprehensive guide to common tasks performed by system administrators, including installation, customization, and troubleshooting. Expanded coverage of networking and […]
Description In this course you will cover: different types of servers; identification of hardware and software components used in servers; installation of servers in a network environment; configuring servers and […]
Description This course covers network defense and incident response methods, tactics, and procedures that are in alignment with industry frameworks such as NIST 800-61r2 (Computer Security Incident Handling Guide), US-CERT's […]
Description In this course, students will learn to plan and execute an endpoint deployment strategy using contemporary deployment techniques and implementing update strategies. The course introduces essential elements of modern […]